Understanding Bill Acceptor Hacks
Bill acceptors are critical components in various automated transaction machines, such as vending machines and arcade gaming systems. A bill acceptor hack supplier specializes in providing devices that can potentially exploit vulnerabilities in bill acceptors to manipulate the credit counting system. It's important to note that discussing bill acceptor hacks is for informational purposes only, and such practices are illegal and unethical.
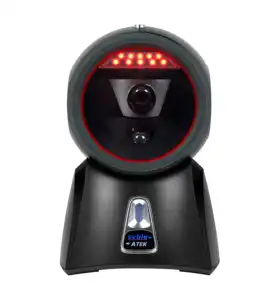
Types of Bill Acceptors
Suppliers may offer a range of bill acceptors designed for different applications. These include stacker bill acceptors, which collect and store bills inside the machine, and stackerless bill acceptors, which allow bills to pass through and return to the user. Each type comes with its own set of security features and mechanisms to detect authenticity and prevent fraudulent activities.
Features of Bill Acceptors
A legitimate bill acceptor supplier will focus on the security and efficiency of their products. Modern bill acceptors are equipped with advanced optical and magnetic sensors to accurately validate currency, multi-currency acceptance for international use, and easy-to-use interfaces for programming and maintenance. These features ensure reliable operation in various service environments.
Materials and Construction
The construction of bill acceptors is another critical aspect. High-quality materials such as robust plastics and metals are used to withstand frequent use and potential tampering. The durability of these materials ensures the longevity of the bill acceptors, making them a reliable component in transactional devices.
Advantages of Secure Bill Acceptors
Reliable bill acceptors offer numerous advantages, including increased transaction speed, reduced human error, and enhanced customer satisfaction. Suppliers aim to provide bill acceptors that support these benefits while maintaining a strong defense against any form of hacking or tampering.
Choosing a Bill Acceptor Supplier
When selecting a bill validator supplier, it's essential to consider the reputation and reliability of the products offered. A supplier should provide a range of bill acceptors that cater to various industries and applications, ensuring compatibility and security for all users.









































 浙公网安备 33010002000092号
浙公网安备 33010002000092号 浙B2-20120091-4
浙B2-20120091-4